Coding & Automation for CyberSecurity
Automation in cybersecurity is not about building software — it is about reducing analyst workload, improving detection speed, and increasing response accuracy.
Practical scripting and automation for SOC, Blue Team, Red Team and Network Security roles.
This section focuses on practical scripting used in real-world security operations, including detection engineering, SOC workflows, incident response, and network automation.
Coding
Providing Resources for system protection, incident response guides, and interactive for enhanced security.


Coding & Automation
Coding tips, tutorials, and an interactive code editor to boost your programming skills.


Coming Soon...
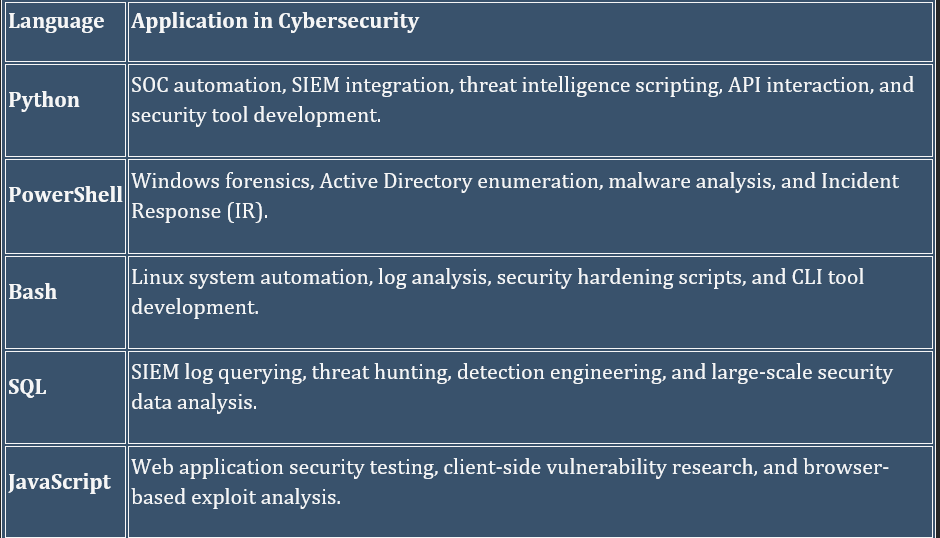
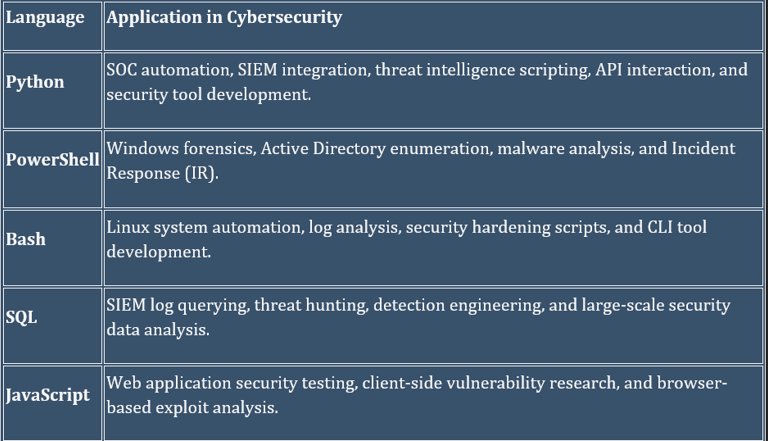
🔍 Detection Engineering
Logic and scripting to identify malicious behavior across logs, endpoints, and networks.
Use Cases: Brute-force login detection, suspicious PowerShell execution, and log anomaly detection.
Tools: Python, SQL, Regex, YAML.
🛡️ SOC Operations
Streamlining repetitive analyst tasks to focus on high-fidelity alerts.
Use Cases: IOC enrichment, automated log parsing, and alert prioritization.
Tools: Python, PowerShell, Bash, SQL.
🚨 Incident Response
Supporting rapid investigation, containment, and recovery phases.
Use Cases: Automated memory triage, bulk log collection, and forensic timeline generation.
Tools: PowerShell, Bash, Python.
🔒 Defensive Security
Continuous system hardening and compliance monitoring.
Use Cases: Automated firewall audits and patch compliance reporting.
Tools: PowerShell, Bash, Python.
⚔️ Offensive Security
Controlled ethical testing and reconnaissance automation.
Use Cases: Automated port scanning and credential/password spraying.
Tools: Python, Bash, PowerShell.
🌐 Network Automation
Programmatic configuration and infrastructure management.
Use Cases: VLAN deployment and ASA firewall rule automation.
Tools: Python, Bash.
Get In Touch With Us
Connect with us for inquiries, support, and collaboration opportunities in cybersecurity, coding, and ethical hacking. We’re here to help!
Contact
plorify
Support
cyberhelp@cybercodinghacker.com
